Tech
Popular cyber security threats to be aware of in 2024

The technology continues to advance at a rapid pace, so too do the methods and strategies employed by cybercriminals. In current times, the digital landscape is fraught with an array of ever-evolving cyber threats, posing significant risks to individuals, businesses, and governments. From sophisticated phishing schemes to ransomware attacks targeting critical infrastructure, awareness of common cyber security threats has never been more crucial. This blog will delve into some of the most prevalent dangers lurking in cyberspace this year, equipping you with the knowledge needed to bolster your defenses and navigate the digital world with greater confidence.
A career in cybersecurity offers an exciting path for those with a passion for technology and a desire to protect against digital threats. As cyber-attacks become increasingly sophisticated and pervasive, the demand for skilled and qualified cybersecurity professionals continues to soar. Pursuing a cyber security certification course can provide aspiring professionals with the necessary knowledge and skills needed to thrive in this rapidly evolving field. These courses offer comprehensive training in areas including, network security, ethical hacking, and incident response, equipping individuals with the expertise to detect, prevent, and mitigate cyber threats. With organizations across all sectors investing heavily in cybersecurity measures, certified professionals are well-positioned to secure lucrative positions and contribute to safeguarding the digital infrastructure of today and tomorrow.
What is cyber security?
Cybersecurity typically refers to the practice of protecting computer systems, networks, and data from unauthorized access, cyber attacks, and other digital threats. It also encompasses a range of techniques, technologies, and processes designed to safeguard information and ensure the confidentiality, integrity, and availability of data. This field encompasses various areas, including network security, data encryption, threat detection and response, vulnerability management, and user awareness training. Cybersecurity professionals work to identify potential vulnerabilities, implement preventative measures, and respond to incidents effectively to mitigate risks and protect against cyber threats in an increasingly interconnected digital world.
What are cyber security threats?
Cybersecurity threats are malicious activities and tactics designed to exploit computer systems, networks, and data vulnerabilities. These threats include malware such as viruses, worms, and ransomware, which can infiltrate and damage systems or steal sensitive information. Phishing attacks involve tricking users into revealing personal or confidential data through deceptive emails or websites. Other threats include denial-of-service (DoS) attacks, where systems are overwhelmed with traffic, and insider threats, where individuals within an organization misuse their access to compromise security. Cybersecurity threats pose significant risks to individuals, businesses, and governments, highlighting the importance of robust security measures and awareness to mitigate potential damage and breaches.
Common cyber security threats
Phishing: Phishing attacks involve cybercriminals sending deceptive emails or messages impersonating trusted entities, such as banks or government agencies. These messages often contain urgent requests or enticing offers, aiming to trick individuals into divulging sensitive information like usernames, passwords, or financial details. Phishing can also lead victims to malicious websites or prompt them to download malware-infected attachments.
Malware: Malware, short for malicious software, encompasses a broad category of harmful programs designed to infiltrate and compromise computer systems or networks. This includes viruses, which attach themselves to legitimate files and replicate when executed; worms, which spread independently across networks; trojans, which disguise themselves as legitimate software to trick users into installing them; and ransomware, which encrypts files or systems and demands payment for their release.
Denial-of-Service (DoS) Attacks: DoS attacks aim to disrupt the normal functioning of a system or network by flooding it with excessive traffic or requests, rendering it inaccessible to legitimate users. Distributed Denial-of-Service (DDoS) attacks involve multiple compromised devices, known as a botnet, coordinated to overwhelm the target. DoS attacks can impact critical services, such as websites or online services, causing financial losses and reputational damage.
Insider Threats: Insider threats occur when individuals within an organization, such as employees, contractors, or business partners, misuse their access privileges to intentionally or unintentionally compromise data security. This may involve stealing sensitive information, intentionally leaking confidential data, or inadvertently falling victim to phishing attacks or social engineering tactics. Insider threats pose significant challenges for organizations, as they can bypass traditional security measures and often require a combination of technical controls and employee awareness training to mitigate.
Man-in-the-Middle (MitM) Attacks: In MitM attacks, cybercriminals intercept communication between two parties, such as a user and a website or two networked devices. By positioning themselves between the communication flow, attackers can eavesdrop on sensitive information or manipulate data exchanges without the knowledge of the legitimate parties. MitM attacks are commonly carried out on unsecured public Wi-Fi networks or through compromised routers.
SQL Injection: SQL injection attacks target web applications that use insecure code to interact with databases. Attackers exploit vulnerabilities in these applications by injecting malicious SQL (Structured Query Language) code into input fields or parameters. Successful SQL injection attacks can bypass authentication mechanisms, extract sensitive data from databases, modify or delete records, and even gain control over the underlying server.
Zero-Day Exploits: Zero-day exploits target vulnerabilities in software or hardware that are previously unknown to the vendor or the public. Cybercriminals exploit these vulnerabilities to launch attacks before a patch or security fix is available, leaving users and organizations vulnerable to exploitation. Zero-day exploits can have severe consequences, as they provide attackers with a window of opportunity to compromise systems and networks without detection or mitigation.
Advanced Persistent Threats (APTs): APTs are sophisticated and stealthy cyber attacks orchestrated by skilled adversaries, such as nation-state actors or organized cybercrime groups. APTs involve a prolonged and targeted campaign aimed at infiltrating and persistently accessing sensitive networks or data. These attacks often employ a combination of advanced techniques, including social engineering, zero-day exploits, and custom malware, making them challenging to detect and mitigate.
Social Engineering: Social engineering tactics exploit human psychology and trust to manipulate individuals into divulging confidential information or performing actions that compromise security. Common social engineering techniques include pretexting (creating a false pretext or scenario to extract information), baiting (luring victims with promises of rewards or benefits), and tailgating (physically or digitally following someone into a restricted area). Social engineering attacks often rely on the exploitation of human curiosity, fear, or willingness to help, making them difficult to defend against solely with technical controls.
Internet of Things (IoT) Vulnerabilities: IoT devices, such as smart home gadgets, industrial sensors, and connected appliances, are increasingly integrated into everyday life and business operations. However, many IoT devices lack robust security measures, making them vulnerable to exploitation by cybercriminals. IoT vulnerabilities can be exploited to gain unauthorized access to devices, compromise user privacy, launch DDoS attacks, or infiltrate corporate networks. Securing IoT devices requires a combination of device hardening, network segmentation, and ongoing monitoring to mitigate risks effectively.
Understanding these common cybersecurity threats is essential for individuals, organizations, and cybersecurity professionals to implement appropriate preventive measures, detection capabilities, and incident response strategies to mitigate risks and safeguard against potential cyber attacks.
Conclusion
The landscape of cybersecurity threats in 2024 is dynamic and ever-evolving, presenting significant challenges to individuals, businesses, and governments worldwide. Being aware of common threats such as phishing, malware, and insider attacks is essential for implementing effective defense strategies. Moreover, pursuing a cyber security certification course offers invaluable expertise and skills necessary to combat these threats proactively. By gaining proficiency in areas such as network security, ethical hacking, and incident response, individuals can position themselves for lucrative career opportunities in the growing cybersecurity domain. Investing in cybersecurity education not only enhances personal and professional development but also contributes to strengthening global cybersecurity resilience in an increasingly digital world.
Tech
Iversær – The Intricate Tapestry of Humanity

Introduction
In a world teeming with diverse cultures, unique perspectives, and varying backgrounds, the term “iversær” comes to the forefront as a beacon of unity and understanding. But what does iversær signify? How does it intertwine with the broader themes of diversity, inclusion, and human connection? This guide explores the essence of iversær, its real-world applications, and its potential to shape a vibrant and inclusive future.
Define “iversær”
Iversær is a concept that encapsulates the beauty of diversity, the richness of individual uniqueness, and the importance of fostering a sense of belonging among all people. Rooted in the idea that every person contributes to the intricate tapestry of humanity, iversær embraces differences as strengths rather than obstacles.
The Essence of Iversær
Core Values and Principles
At its core, iversær embodies values such as:
- Inclusivity: Welcoming all individuals irrespective of their backgrounds.
- Respect: Honoring the differences and unique qualities of each person.
- Empathy: Understanding and sharing the feelings of others.
- Equity: Ensuring fair treatment, opportunities, and advancement for all.
Importance of Individual Uniqueness
Every individual’s uniqueness contributes to a richer, more vibrant society. Recognizing and celebrating these differences fosters a sense of belonging and community, empowering people to bring their full selves to every aspect of life.
Contribution to Society
Iversær contributes to society by:
- Enhancing Creativity and Innovation: Diverse perspectives lead to more creative solutions and innovative ideas.
- Strengthening Communities: Inclusive communities are more cohesive, resilient, and supportive.
- Promoting Social Harmony: Understanding and empathy reduce conflicts and build stronger relationships.
Iversær in Action
Real-world Examples
- Communities: Neighborhoods that celebrate diverse cultural festivals, encouraging cross-cultural interactions.
- Organizations: Companies implementing diversity and inclusion programs that promote a diverse workforce.
- Cultures: Countries with policies supporting multiculturalism and integration.
Case Studies
- Tech Industry: Companies like Google and Apple investing in diversity initiatives, resulting in innovative products and inclusive work environments.
- Education Sector: Schools adopting inclusive curricula that reflect the diverse backgrounds of students, fostering a culture of acceptance and mutual respect.
Challenges and Opportunities
- Challenges:
- Resistance to Change
- Unconscious Bias
- Inequality and Discrimination
- Opportunities:
- Creating Inclusive Policies
- Promoting Cross-cultural Understanding
- Leveraging Technology for Inclusivity
Cultivating Iversær
Strategies for Individuals
- Self-Education: Learn about different cultures, histories, and perspectives.
- Active Listening: Listen to understand, not just to respond.
- Inclusive Behavior: Practice inclusivity in daily interactions, both personally and professionally.
Promoting Iversær in Organizations
- Inclusive Hiring Practices: Ensure diverse representation in the hiring process.
- Employee Resource Groups: Support groups that represent various demographics within the organization.
- Ongoing Training: Provide continuous education on diversity, inclusion, and equity.
Role of Education and Awareness
- Inclusive Curriculum: Integrate diverse perspectives into educational content.
- Awareness Campaigns: Run campaigns to educate the public about the importance of diversity and inclusion.
- Community Engagement: Involve communities in dialogues and activities that promote iversær.
Iversær and the Future
Shaping a Better World
The potential of iversær to shape a better world lies in its ability to bring people together, bridging gaps and fostering understanding. By championing diversity, we can create a more equitable and harmonious society.
Emerging Trends and Innovations
- AI and Inclusion: AI tools that help mitigate biases in hiring and decision-making processes.
- Global Collaboration: International partnerships focusing on global challenges through diverse perspectives.
Call to Action
Become a champion of iversær. Start by making small changes in your daily life, advocating for inclusivity in your community, and supporting policies that promote diversity and equity.
FAQs
1. What does “iversær” mean?
Iversær is a term that represents the celebration of diversity, inclusivity, and the unique qualities of each individual.
2. How can I promote iversær in my workplace?
You can promote iversær by implementing inclusive hiring practices, supporting employee resource groups, and providing ongoing training on diversity and inclusion.
3. Why is iversær important in education?
Iversær in education fosters a culture of acceptance and mutual respect, helping students appreciate diverse perspectives and build empathy.
4. What are some real-world examples of iversær?
Examples include diverse cultural festivals in communities, diversity initiatives in organizations like Google, and inclusive curricula in schools.
5. How can technology support iversær?
Technology can support iversær by providing AI tools that reduce biases, facilitating global collaboration, and offering platforms for inclusive communication.
YOU MAY ALSO LIKE
Ultimate Guide to Rssawee for Environmental and Adventure Enthusiasts
Conclusion
In summary, iversær is not just a concept but a way of life that enriches our society. By understanding its essence, witnessing its impact in action, and actively cultivating it in our lives, we can contribute to a world where everyone feels valued and included.
Tech
Harmonicode: Unveiling the Mystery of Music Through Play

Introduction
Have you ever wondered how music is created? Is there a secret code that unlocks the magic of melodies? If these questions pique your curiosity, you’re in for a treat! Enter Harmonicode, a revolutionary product that makes learning music theory fun and engaging for all ages. Whether you’re an environmental enthusiast, an adventure lover, or a small business owner, Harmonicode has something to offer.
What is Harmonicode?
Category and Price
Harmonicode belongs to the Games category and is currently priced at US$120.00. The good news? It’s in stock and ready to bring a world of musical discovery right to your doorstep.
Functionality
Harmonicode is designed to teach music theory concepts in a playful and interactive way. It’s both a physical and digital product, offering a unique blend of tactile and online learning experiences. It transforms what can often be a dry subject into a fun, engaging activity.
Target Audience
Harmonicode is perfect for:
- Aspiring musicians of all ages
- Individuals who want to understand the building blocks of music
- Teachers looking for innovative ways to engage students
- Families wanting to learn together
How Does Harmonicode Work?
Gameplay/Usage
Harmonicode can be used as a game, a puzzle, or a musical instrument simulation. Here’s how to get started:
- Unbox Your Harmonicode Kit: Inside, you’ll find a set of beautifully designed cards and access to the Harmonicode digital platform.
- Setup: Follow the instructions to set up your physical or virtual game space.
- Begin Playing:
- Music Theory Fundamentals: Learn scales, chords, and intervals through interactive challenges.
- Interactive Gameplay: Engage with puzzles that require you to apply music theory concepts to progress.
- Track Progress: Use the built-in progress tracker to monitor your learning.
Key Features
Harmonicode stands out because of its unique features:
- Teaches Music Theory Fundamentals: Covers scales, chords, intervals, and more.
- Interactive and Engaging Gameplay: Keeps users motivated and eager to learn.
- Suitable for Various Skill Levels: Whether you’re a beginner or more advanced, Harmonicode adapts to your level.
- Additional Features:
- Progress tracking
- Challenges and rewards
- Community interaction
Benefits of Using Harmonicode
Enhanced Musical Understanding
- Strong Foundation: Develop a solid understanding of music theory.
- Skill Improvement: Improve your composition and performance skills.
- Deeper Appreciation: Unlock a deeper appreciation for music by understanding its building blocks.
Fun and Engaging Learning
- Less Intimidating: Makes learning music theory less daunting and more fun.
- Motivational: Interactive gameplay keeps you engaged and motivated.
- Family Activity: Suitable for all ages, making it a great family activity.
Social Proof and Credibility
User Testimonials
Don’t just take our word for it—here’s what some of our satisfied users have to say:
- Steve, USA: “I can’t believe that Harmonicode is free! It’s ideal for making sure all of my work is polished and professional.”
- Penny, Australia: “I use this product almost every day! The complex rephrasing component complements grammar products like Grammarly and LanguageTool really well. Great job!”
Awards and Recognition
Harmonicode has received several industry awards for its innovative approach to music education, reinforcing its credibility and effectiveness.
FAQs
- What is Harmonicode?
- Harmonicode is an interactive product designed to teach music theory concepts in a fun and engaging way, suitable for all ages and skill levels.
- How much does Harmonicode cost?
- Harmonicode is priced at US$120.00 and is available in stock, ready to bring musical discovery to your doorstep.
- Who is the target audience for Harmonicode?
- Harmonicode is perfect for aspiring musicians, individuals wanting to learn music theory, teachers, and families looking for a fun, educational activity.
- What features does Harmonicode offer?
- Harmonicode offers music theory fundamentals, interactive gameplay, progress tracking, challenges, rewards, and community interaction.
- How does Harmonicode enhance musical understanding?
- By providing a strong foundation in music theory, improving composition and performance skills, and fostering a deeper appreciation for music.
YOU MAY ALSO LIKE
Engaging Dental Websites: Best Practices for Attracting and Retaining Patients
Conclusion
Recap the Value Proposition
Harmonicode is not just a tool; it’s a gateway to unlocking the mysteries of music theory through play. With its interactive gameplay, comprehensive learning modules, and suitability for all ages, it’s the perfect addition to any music enthusiast’s toolkit.
Tech
Kannák – The Epitome of Strength and Functionality
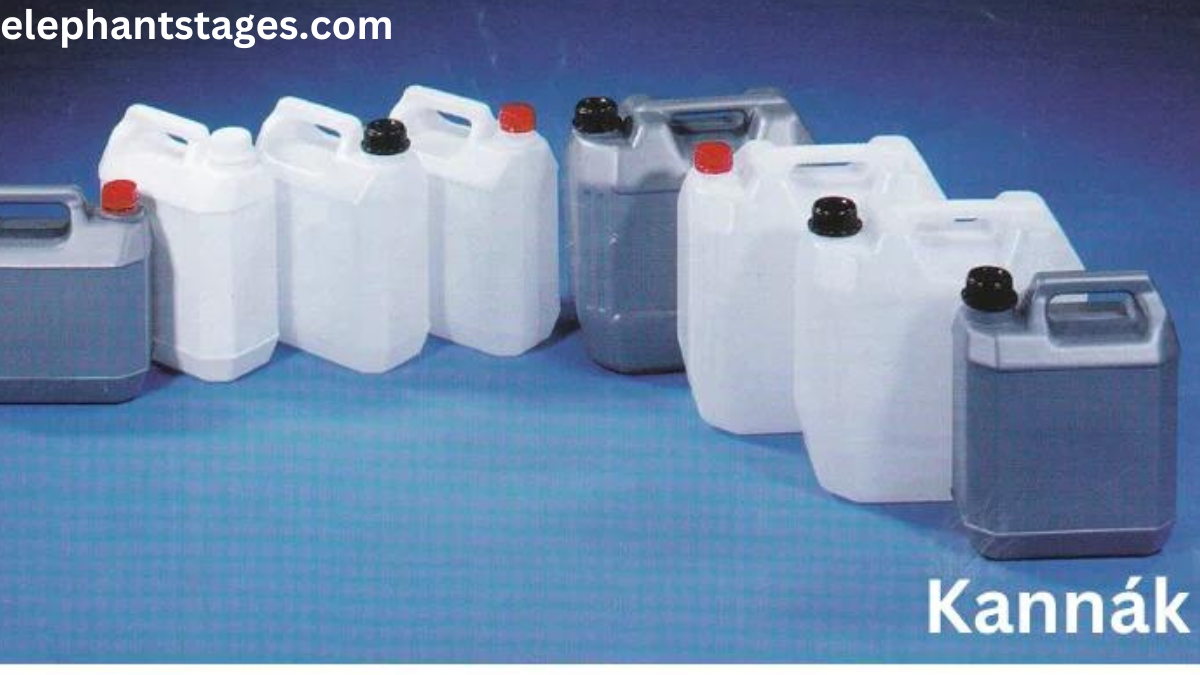
Introduction
Imagine a world where every tool, every piece of equipment, and every resource you use embodies the perfect balance of strength and functionality. What if there were a term that encapsulated this ideal? Enter Kannák.
What is Kannák?
Kannák, pronounced “kan-ak,” stands as a testament to the fusion of power and utility. Though the term may be unfamiliar to some, its implications are universally relevant. Kannák represents not just physical robustness, but also the relentless efficiency and effectiveness needed to overcome challenges and achieve success.
The Essence of Kannák
Strength
Physical Attributes
- Durability: Kannák is built to last. Whether it’s withstanding the harshest weather conditions or enduring rigorous use, Kannák remains unyielding.
- Resilience: Beyond mere durability, Kannák can bounce back from setbacks, maintaining its integrity and functionality.
- Resistance: Kannák is designed to resist wear and tear, corrosion, and other forms of degradation.
Metaphorical Strength
- Symbol of Power: Kannák isn’t just about physical strength. It symbolizes the power to push through obstacles and achieve greatness.
- Courage: Embodying Kannák means having the bravery to face challenges head-on.
- Determination: With Kannák, there’s an unwavering commitment to reach goals, no matter the difficulty.
Functionality
Practical Applications
- Versatility: Kannák can be used in various contexts, from everyday tools to specialized equipment.
- Efficiency and Effectiveness:
- Optimal Performance: Kannák delivers results with minimal effort and maximum impact.
- User-Friendly: Even the most complex versions of Kannák are designed for ease of use.
Kannák in Various Domains
Kannák in Adventure Gear
For adventure enthusiasts, Kannák could be the defining trait of their gear.
- Backpacks:
- Strength: Reinforced stitching, durable materials.
- Functionality: Multiple compartments, ergonomic design.
- Tents:
- Strength: Weather-resistant fabrics, sturdy poles.
- Functionality: Easy setup, compact storage.
Kannák in Small Business Tools
Small business owners often seek tools that exemplify Kannák.
- Software Solutions:
- Strength: Robust security features.
- Functionality: Intuitive interfaces, comprehensive analytics.
- Marketing Tools:
- Strength: Reliable servers, high uptime.
- Functionality: Customizable templates, user-friendly dashboards.
Kannák and Related Concepts
Comparisons
How Kannák differs from similar terms/products:
- Quality vs. Quantity:
- Kannák focuses on excellence, ensuring each product or resource is of the highest quality, whereas quantity-focused options may prioritize volume over value.
Complementary Elements
What enhances the capabilities of Kannák:
- Technological Integrations:
- Smart Features: IoT (Internet of Things) can enhance Kannák products, providing real-time updates and remote control capabilities.
- Sustainable Practices:
- Eco-Friendly Materials: Using materials that are both strong and environmentally friendly enhances the overall value of Kannák.
The Future of Kannák
Innovations
- Advanced Materials:
- Nanotechnology can further enhance the strength and durability of Kannák products.
- AI Integration:
- Predictive Maintenance: AI can predict when a Kannák product needs servicing, ensuring it remains functional for longer.
Trends
How Kannák aligns with current or future trends:
- Sustainability:
- Eco-conscious consumers are increasingly demanding products that are not only strong and functional but also environmentally responsible.
- Customization:
- Personalized Solutions: The future of Kannák includes bespoke products tailored to individual needs and preferences.
Five Most Searched FAQs on Google and Answers
- What does Kannák mean?
- Kannák symbolizes the perfect balance of strength and functionality, combining physical robustness with relentless efficiency.
- How is Kannák applied in adventure gear?
- In adventure gear, Kannák is embodied through features like reinforced stitching in backpacks and weather-resistant fabrics in tents.
- Why is Kannák important for small business tools?
- Small business tools with Kannák offer robust security and user-friendly interfaces, ensuring reliability and efficiency.
- What innovations enhance Kannák products?
- Innovations like nanotechnology and AI integration enhance the strength, durability, and predictive maintenance of Kannák products.
- How is Kannák related to sustainability?
- Kannák aligns with eco-conscious trends by using strong, environmentally friendly materials, catering to the growing demand for sustainable products.
YOU MAY ALSO LIKE
Why RAID Remains a Preferred Choice for Modern Data Centers
Conclusion
Kannák stands as a beacon of strength and functionality, applicable across various domains and essential for overcoming life’s challenges. From adventure gear to small business tools, Kannák ensures optimal performance and durability. As we look to the future, innovations in material science and technology will only enhance Kannák’s relevance and impact.
-

 News3 months ago
News3 months agoWhat Are the Biggest Challenges in Marine Construction Projects in Australia?
-

 Health4 months ago
Health4 months agoUnderstanding Ftmç: Gender-Affirming Surgery
-

 Fashion3 months ago
Fashion3 months agoAttractive Beach Dresses: Elevate Your Look with These Ideas
-

 Tech3 months ago
Tech3 months agoAiyifan: Unveiling the Genie of Technological Revolution
-

 Business3 months ago
Business3 months agoHow Professional Concrete Cleaning Wins Repeat Business
-

 Tech4 months ago
Tech4 months agoThe Ultimate Guide to the Geekzilla Podcast: Diving into the Heart of Geekdom
-

 Pets2 months ago
Pets2 months agoPawsitively Perfect: The Types of Dog Harness Bundle for Your Furry Friend
-

 Health3 months ago
Health3 months agoDesk Job Dilemma: Tips for Back Pain Relief
